Arkansas Information Technology Service Agreement (AITA) is a legally binding contract between a service provider and a client in the state of Arkansas regarding the provision of information technology services. This agreement outlines the terms and conditions under which the services will be delivered, ensuring clarity and protection for both parties involved. AITA covers a wide range of IT services that may include, but are not limited to: 1. System Implementation and Maintenance: This type of agreement includes the planning, installation, configuration, and ongoing support of software systems or hardware infrastructure. It outlines the responsibilities of the service provider in terms of system management, updates, data backups, and disaster recovery. 2. Network Services: AITA can also pertain to the management and maintenance of computer networks, including local area networks (LAN) and wide area networks (WAN). It defines the scope of services, such as network monitoring, security enhancements, troubleshooting, and performance optimization. 3. Cloud Computing Services: With the increasing popularity of cloud-based solutions, AITA can cover agreements related to the setup, management, and support of cloud computing environments. This includes virtual server provisioning, data storage, software as a service (SaaS) implementation, and other cloud-related services. 4. Help Desk and Technical Support: Service agreements can also focus on providing IT support, including a help desk for end-users. This entails addressing technical issues, providing remote assistance, answering questions, and resolving any IT-related problems that may arise. 5. Software Development and Customization: AITA may encompass agreements for software development or customization, where the service provider is contracted to build or modify software applications based on the client's specific requirements. 6. Security Services: In a world with increasing threats to data and online security, AITA can incorporate security-focused agreements, covering services such as vulnerability assessments, penetration testing, security incident response, and the implementation of security protocols. AITA typically includes key clauses such as: a. Service Level Agreements (SLAs): These outline the specific performance levels and metrics that the service provider must meet. SLAs usually cover aspects like response times, uptime guarantees, and resolution times for issues. b. Confidentiality and Data Protection: This clause ensures that both parties agree to protect any confidential or sensitive information shared during the course of the agreement. It may also address compliance with relevant data protection regulations. c. Intellectual Property Rights: This establishes ownership of any intellectual property created or utilized during the provision of services, specifying whether ownership remains with the client or is transferred to the service provider. d. Termination and Renewal: This section outlines the procedures for termination of the agreement by either party, including notice periods and conditions under which termination can occur. It may also address renewal terms if the client wishes to continue the services. AITA aims to establish a comprehensive understanding between the service provider and the client, ensuring a mutually beneficial relationship and the delivery of high-quality IT services.
Arkansas Information Technology Service Agreement
Description
How to fill out Arkansas Information Technology Service Agreement?
Discovering the right lawful file format can be quite a have a problem. Needless to say, there are a lot of web templates available on the Internet, but how would you find the lawful form you require? Take advantage of the US Legal Forms internet site. The service gives a huge number of web templates, such as the Arkansas Information Technology Service Agreement, that you can use for company and private needs. Every one of the types are checked out by experts and meet state and federal specifications.
When you are already registered, log in to the bank account and click the Acquire switch to get the Arkansas Information Technology Service Agreement. Make use of your bank account to appear through the lawful types you possess purchased in the past. Proceed to the My Forms tab of your bank account and obtain one more copy of the file you require.
When you are a brand new consumer of US Legal Forms, listed below are easy directions so that you can comply with:
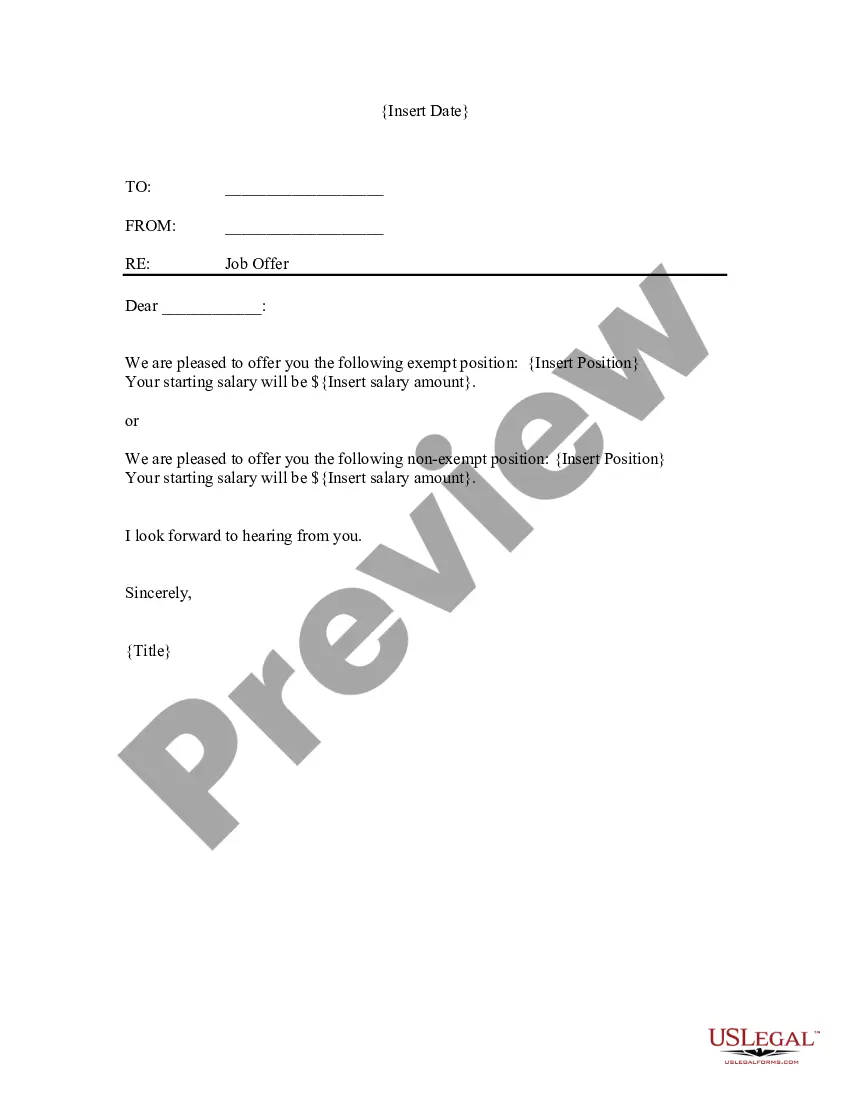
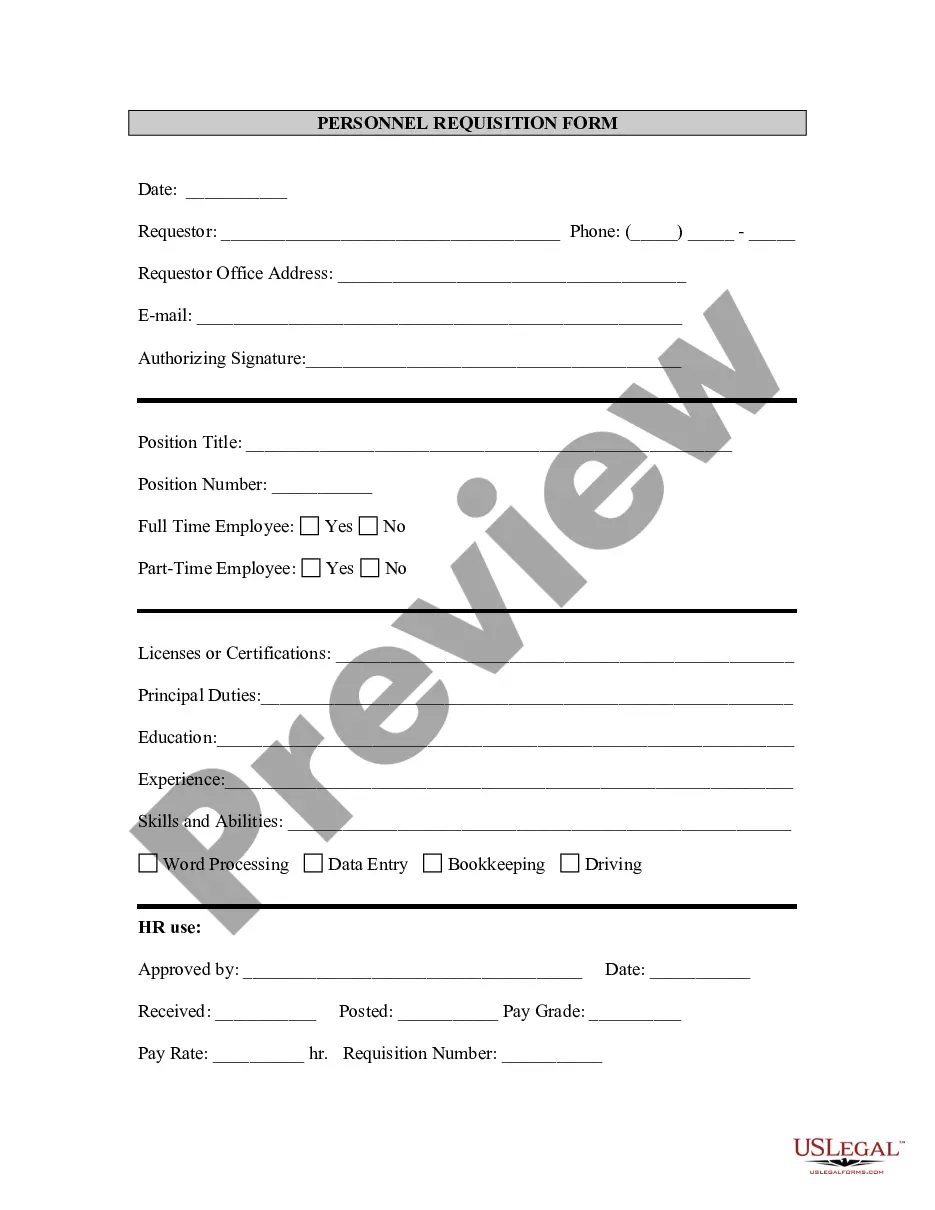
- Initial, ensure you have selected the right form for the town/county. You can look over the form using the Review switch and browse the form explanation to guarantee this is basically the right one for you.
- When the form will not meet your preferences, use the Seach area to get the proper form.
- Once you are certain that the form is acceptable, select the Purchase now switch to get the form.
- Opt for the prices prepare you want and enter in the needed information. Design your bank account and purchase the order utilizing your PayPal bank account or Visa or Mastercard.
- Pick the document structure and acquire the lawful file format to the device.
- Full, revise and print out and sign the obtained Arkansas Information Technology Service Agreement.
US Legal Forms is definitely the largest local library of lawful types in which you can find a variety of file web templates. Take advantage of the service to acquire appropriately-created papers that comply with state specifications.