Title: Iowa's Detailed and Specific Policy Regarding Use of Company Computers Introduction: In the state of Iowa, companies have implemented a comprehensive policy governing the use of company computers. This policy ensures that employees utilize these devices in a responsible and productive manner, while safeguarding the company's security and assets. This document aims to provide a detailed overview of Iowa's specific policies related to the use of company computers, including various types that may exist. 1. General Guidelines: Iowa's policy emphasizes the responsible and professional use of company computers, urging employees to utilize them solely for business-related purposes. Personal use of these devices should be limited to breaks and non-working hours, following specific guidelines outlined by the company. 2. Internet and Email Usage: Iowa's policy includes directives regarding internet and email usage, stipulating that employees should refrain from browsing irrelevant websites during working hours. It emphasizes the importance of refraining from accessing inappropriate, offensive, or illegal content, thus maintaining a professional environment. Employees are expected to use company email accounts exclusively for business purposes. 3. Confidentiality and Security Measures: Iowa's policy highlights the criticality of data security and confidentiality. Employees are required to follow strict protocols, such as creating strong passwords, regularly updating antivirus software, and refraining from sharing sensitive information both internally and externally without proper authorization. Unauthorized software installation is strictly prohibited. 4. Social Media Usage: Under Iowa's policy, employees are guided on the responsible use of social media platforms while representing the company. Guidelines instruct employees to refrain from posting defamatory, discriminatory, or confidential information related to the company. The policy may also outline specific steps to be taken when an employee's social media account identifies themselves as an employee of the company. 5. BYOD (Bring Your Own Device) Policy: Some Iowa companies may have a specific policy outlining the use of personal devices for work-related activities. This allows employees to use their own computers, laptops, or smartphones for work while maintaining compliance with security and data protection measures. The BYOD policy ensures that employees understand their responsibilities regarding device security and data privacy. 6. Monitoring and Enforcement: To uphold the policy, Iowa companies may employ monitoring systems to identify any policy violations. Employees should be aware that their computer activities can be monitored, and appropriate action will be taken if any misconduct is observed. The policy may include disciplinary measures, such as warnings, suspensions, or even termination of employment. Conclusion: Iowa's detailed and specific policy regarding the use of company computers prioritizes responsible, secure, and professional use of these devices. It aims to protect company resources, maintain data confidentiality, and promote an environment conducive to productivity. Employees must adhere to these policies, ensuring compliance with all outlined guidelines to ensure the overall success and security of the company.
Iowa Detailed and Specific Policy with Regard to Use of Company Computers
Description
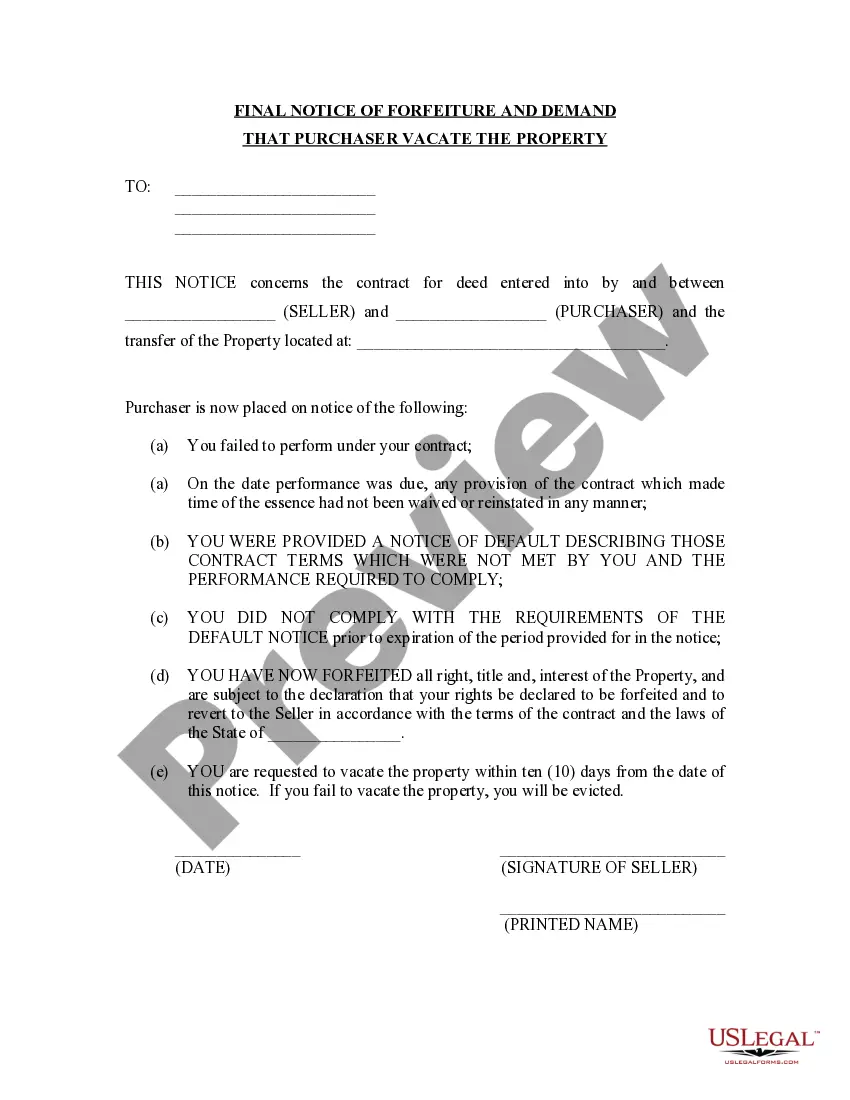
How to fill out Iowa Detailed And Specific Policy With Regard To Use Of Company Computers?
US Legal Forms - one of several greatest libraries of legal types in the United States - offers an array of legal document layouts you can acquire or print out. Using the site, you can get 1000s of types for business and personal uses, categorized by classes, states, or keywords.You can find the most recent variations of types such as the Iowa Detailed and Specific Policy with Regard to Use of Company Computers in seconds.
If you already have a monthly subscription, log in and acquire Iowa Detailed and Specific Policy with Regard to Use of Company Computers from your US Legal Forms catalogue. The Obtain option will show up on each and every develop you view. You get access to all formerly saved types within the My Forms tab of the profile.
If you wish to use US Legal Forms the very first time, here are straightforward directions to help you get started:
- Be sure to have chosen the correct develop for your city/area. Click the Review option to analyze the form`s content. Look at the develop description to actually have selected the proper develop.
- In case the develop doesn`t match your needs, make use of the Search area at the top of the screen to get the the one that does.
- When you are pleased with the shape, validate your choice by clicking the Get now option. Then, select the pricing program you like and offer your qualifications to register to have an profile.
- Process the transaction. Make use of your Visa or Mastercard or PayPal profile to accomplish the transaction.
- Find the structure and acquire the shape in your device.
- Make alterations. Fill up, revise and print out and indication the saved Iowa Detailed and Specific Policy with Regard to Use of Company Computers.
Each design you included in your account does not have an expiration particular date which is yours permanently. So, if you wish to acquire or print out another copy, just go to the My Forms section and click on about the develop you require.
Gain access to the Iowa Detailed and Specific Policy with Regard to Use of Company Computers with US Legal Forms, by far the most considerable catalogue of legal document layouts. Use 1000s of professional and express-particular layouts that fulfill your company or personal demands and needs.