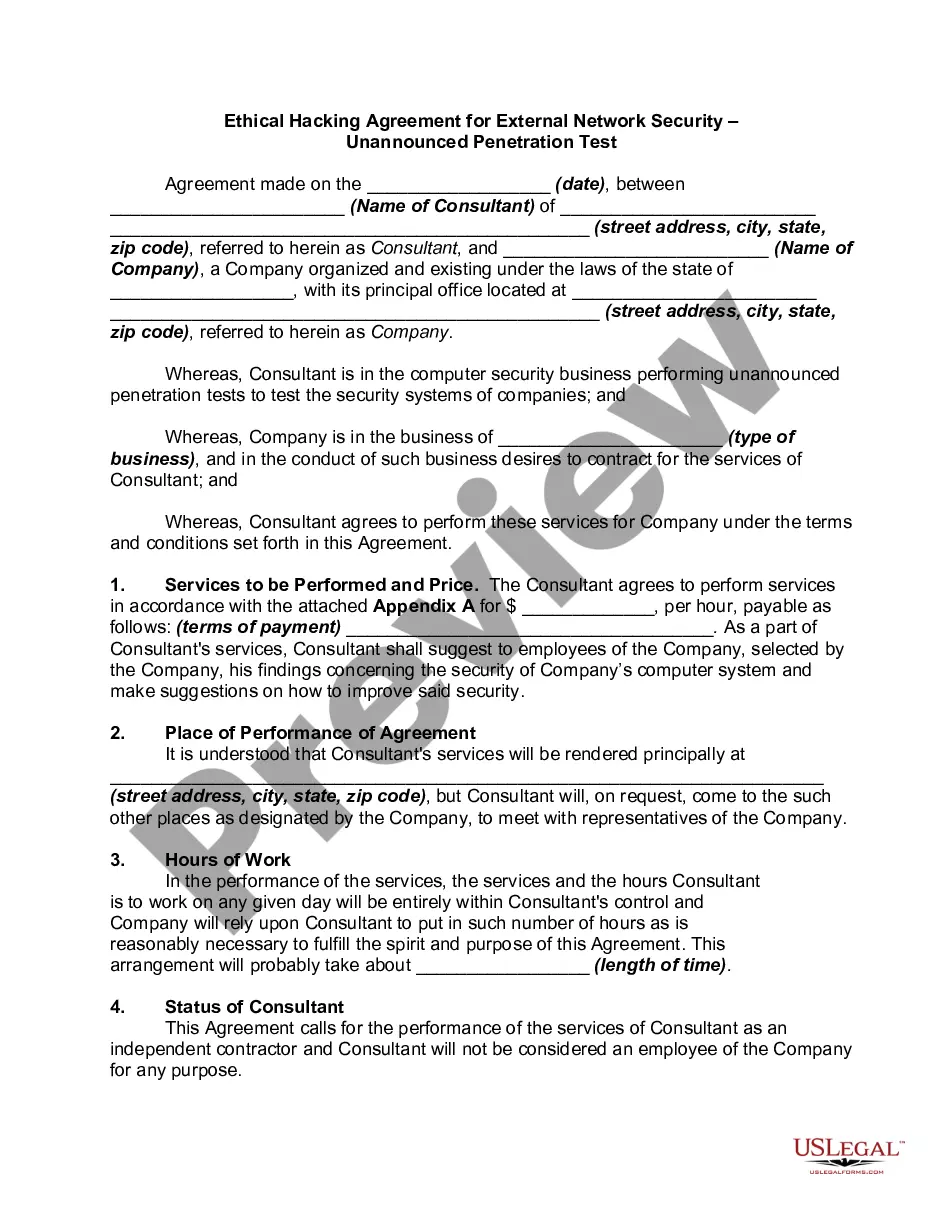
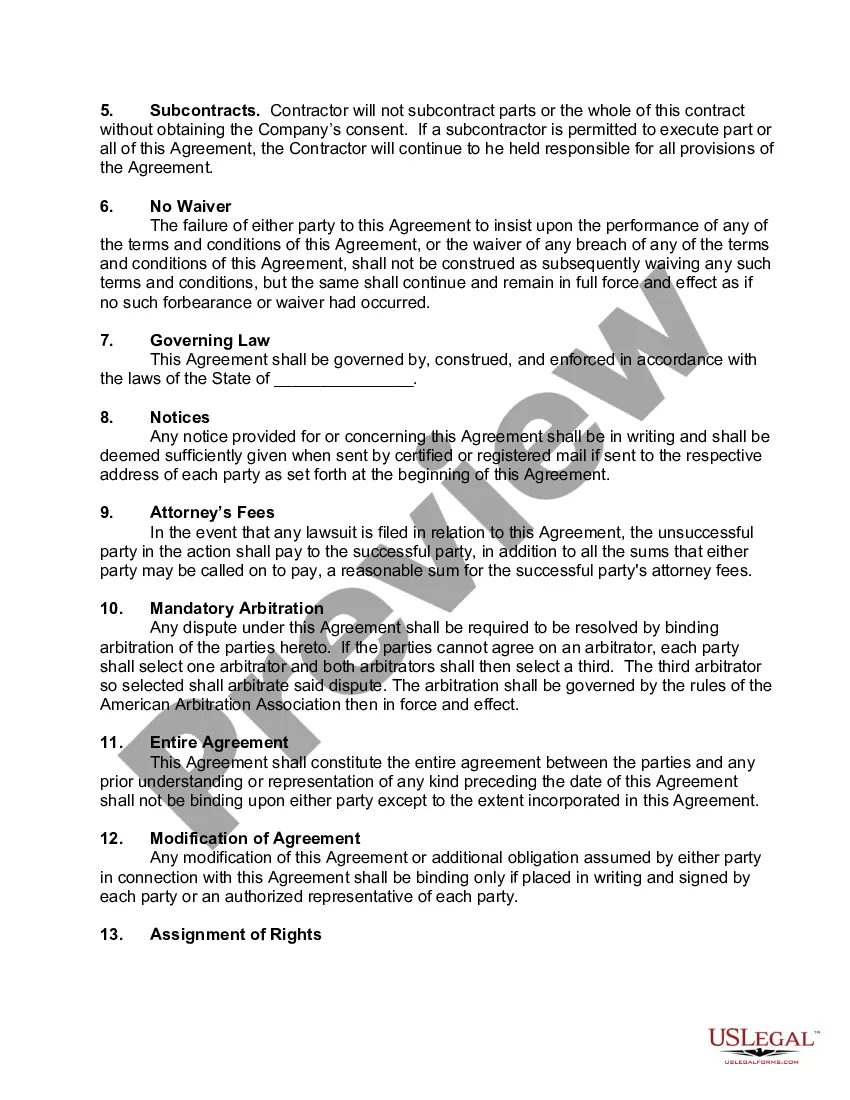
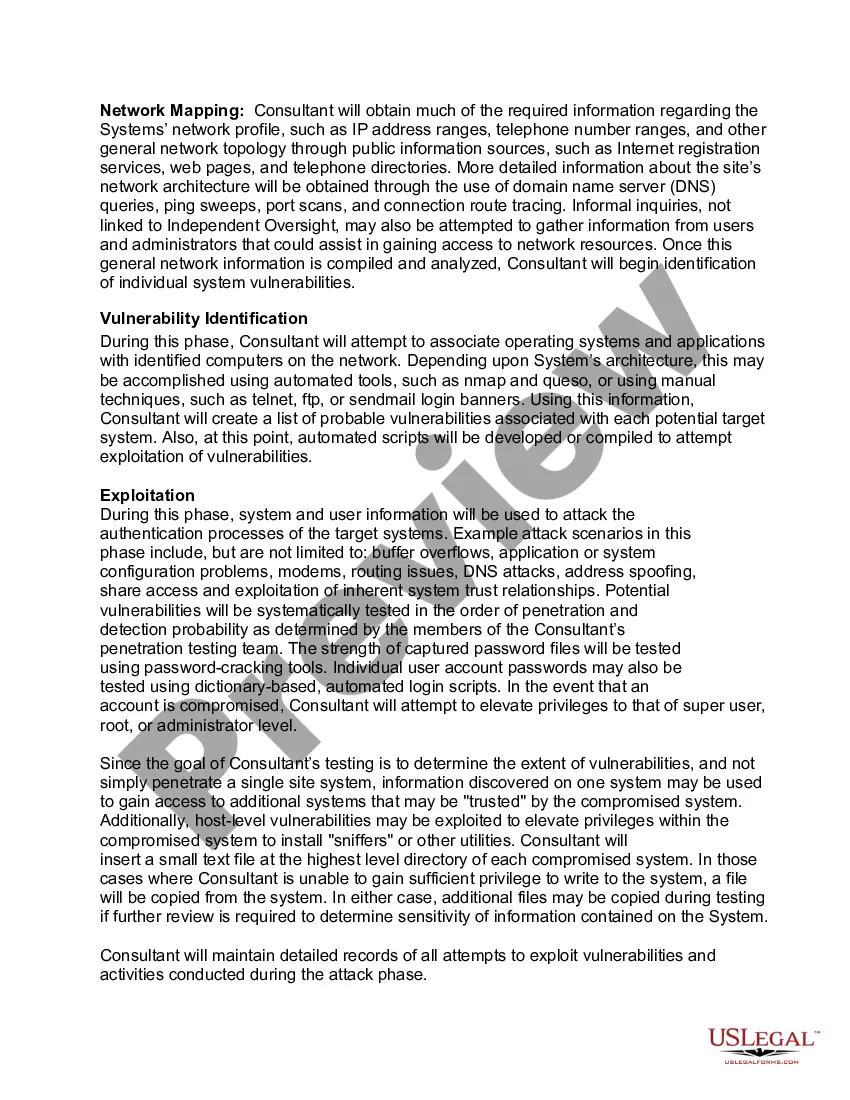
Illinois Ethical Hacking Agreement for External Network Security — Unannounced Penetration Test: The Illinois Ethical Hacking Agreement for External Network Security — Unannounced Penetration Test is a formal contract entered into by organizations located in the state of Illinois to ensure the security and integrity of their external network infrastructure. This comprehensive agreement outlines the terms and conditions for conducting unannounced penetration tests by authorized ethical hackers, commonly referred to as "white hat" hackers, in order to identify vulnerabilities and strengthen the network's security defenses. The primary purpose of this agreement is to establish a legally binding framework between the organization and the security testing company or independent ethical hacker hired to conduct the penetration test. It outlines the scope, limitations, and responsibilities of all involved parties to protect the interests of both the organization and the ethical hacker. The agreement typically consists of the following key components: 1. Scope of Work: This section outlines the specific goals and objectives of the penetration test, including the network systems and components to be evaluated, the permissible actions, and the testing methodologies to be employed. 2. Rules of Engagement: This section defines the rules and limitations that the ethical hacker must adhere to during the penetration test, including the agreed-upon testing hours, targets that are off-limits, and any legal constraints to be taken into consideration. 3. Authorization and Liability: This section clarifies that the organization has authorized the penetration test to be conducted and assumes responsibility for any potential disruptions or damages that may occur during the testing process. It also outlines the ethical hacker's responsibility to exercise due diligence and professionalism while conducting the test. 4. Confidentiality and Non-Disclosure: This section ensures the protection of sensitive information or trade secrets that may be encountered or accessed during the penetration test. Both parties commit to keeping all discovered vulnerabilities, testing methodologies, and test results confidential and agree not to disclose or use them for any unauthorized purposes. 5. Reporting and Documentation: This section outlines the requirements for delivering a comprehensive report detailing the vulnerabilities, exploitation techniques, and remediation recommendations discovered during the penetration test. It also specifies the timeframe for submitting the report and any subsequent discussions or follow-up actions that may be required. Different types of Illinois Ethical Hacking Agreements for External Network Security — Unannounced Penetration Test may include variations in the scope of work, rules of engagement, or specific contractual obligations tailored to meet the unique needs of each organization. These could include agreements for different industries, such as healthcare, finance, or government, as well as agreements that cover specific network components, such as wireless networks or cloud infrastructure. In conclusion, the Illinois Ethical Hacking Agreement for External Network Security — Unannounced Penetration Test is crucial for organizations in Illinois to safeguard their external network infrastructure from potential cyber threats.
Illinois Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test
Description
How to fill out Illinois Ethical Hacking Agreement For External Network Security - Unannounced Penetration Test?
US Legal Forms - one of several largest libraries of legitimate kinds in the USA - delivers a wide array of legitimate document web templates you may down load or print out. Using the website, you will get a large number of kinds for enterprise and individual reasons, categorized by categories, states, or keywords.You can get the newest types of kinds just like the Illinois Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test within minutes.
If you have a subscription, log in and down load Illinois Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test in the US Legal Forms catalogue. The Obtain switch can look on every develop you view. You have accessibility to all formerly acquired kinds within the My Forms tab of your own account.
If you would like use US Legal Forms the first time, listed below are straightforward guidelines to help you started off:
- Make sure you have picked the right develop to your city/area. Click on the Preview switch to review the form`s information. Look at the develop description to ensure that you have chosen the appropriate develop.
- If the develop does not satisfy your requirements, use the Look for industry on top of the screen to discover the one that does.
- Should you be satisfied with the form, validate your selection by clicking on the Purchase now switch. Then, pick the prices strategy you favor and offer your references to register to have an account.
- Method the deal. Make use of your credit card or PayPal account to accomplish the deal.
- Select the formatting and down load the form on the product.
- Make modifications. Complete, edit and print out and signal the acquired Illinois Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test.
Each and every design you included in your bank account lacks an expiry day which is your own property for a long time. So, in order to down load or print out one more backup, just proceed to the My Forms section and click on the develop you require.
Obtain access to the Illinois Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test with US Legal Forms, by far the most substantial catalogue of legitimate document web templates. Use a large number of professional and condition-specific web templates that satisfy your business or individual requirements and requirements.