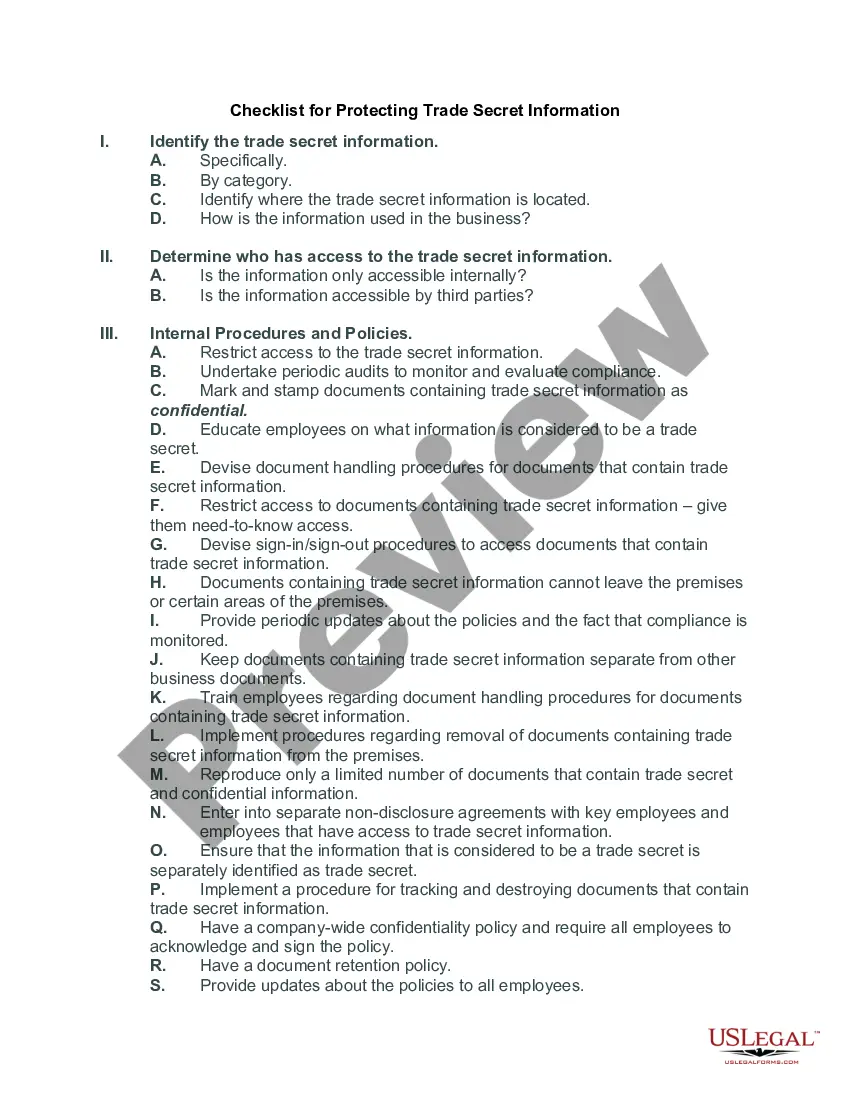
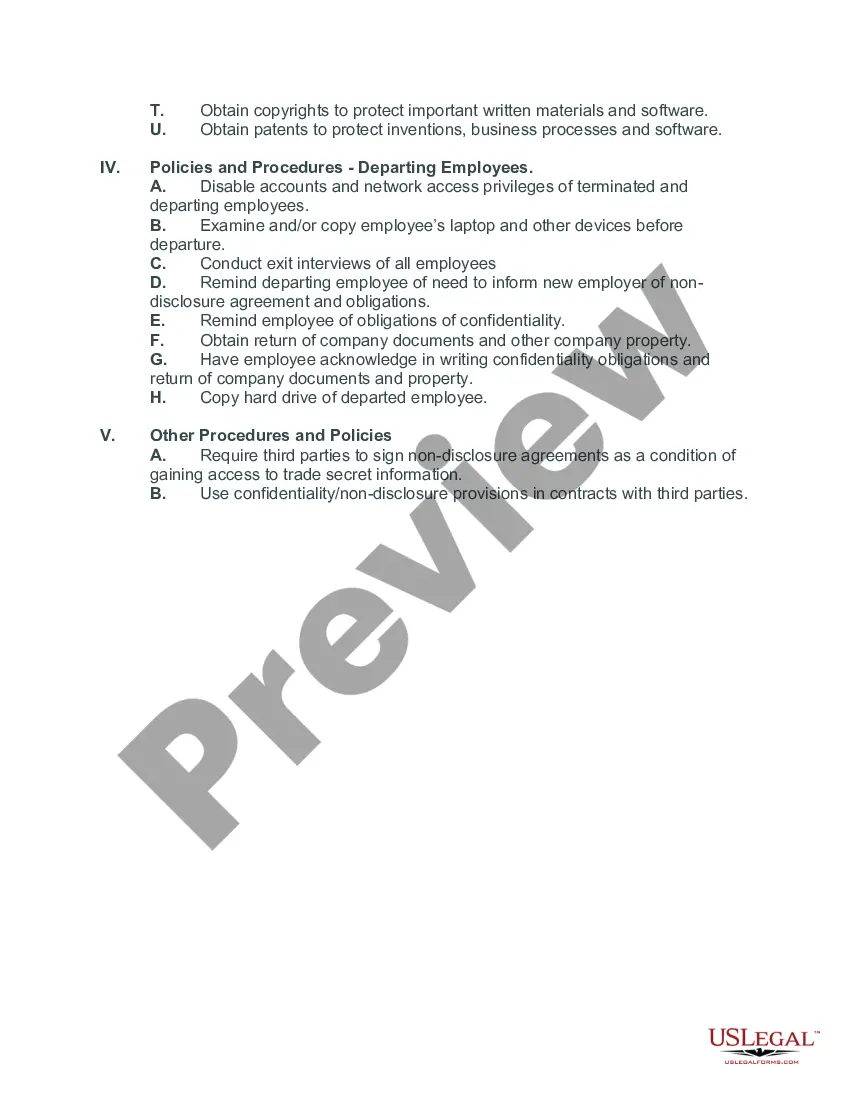
Title: Texas Checklist for Protecting Trade Secret Information — A Comprehensive Guide Keywords: Texas, checklist, protecting, trade secret information, safeguarding, legal aspects, types, intellectual property, non-disclosure agreement, security measures, employee training, litigation, enforcement Introduction: In the state of Texas, protecting trade secret information is of utmost importance for businesses and individuals to maintain a competitive edge and preserve their intellectual property rights. This detailed checklist aims to provide a comprehensive guide to safeguard trade secrets effectively, ensuring legal compliance and minimizing the risk of unauthorized disclosure or misappropriation. Let's explore the key aspects of the Texas Checklist for Protecting Trade Secret Information and understand the different types associated with it. 1. Identification and Classification: a. Identifying trade secrets within your business. b. Classifying different trade secrets based on their importance, value, and vulnerability. 2. Legal Documentation: a. Preparing a Non-Disclosure Agreement (NDA) for employees, contractors, and business partners. b. Including non-compete and non-solicitation clauses within legal agreements. 3. Security Measures: a. Implementing physical security controls, such as restricted access areas and secure storage for sensitive information. b. Establishing robust IT security measures, including firewalls, encryption, password controls, and regular system audits. c. Utilizing confidentiality markings on documents and electronic files. 4. Employee Education and Training: a. Conducting comprehensive training sessions on trade secrets, their identification, protection, and potential consequences of unauthorized disclosures. b. Emphasizing the importance of maintaining confidentiality and adhering to company policies. 5. Restricting Access: a. Limiting access to trade secret information to only authorized personnel. b. Implementing stringent access controls and authentication protocols for sensitive databases and computer networks. c. Maintaining a record of individuals with authorized access. 6. Secure Data Handling: a. Developing clear guidelines for the handling, transmission, and storage of trade secret information both within the company premises and while interacting with external entities. b. Encouraging secure data backup practices to prevent loss or unauthorized access. 7. Regular Audits and Evaluations: a. Conducting periodic assessments to ensure compliance with trade secret protection measures. b. Identifying potential vulnerabilities, updating security protocols, and addressing any deficiencies promptly. 8. Litigation and Enforcing Rights: a. Understanding legal remedies available under the Texas Uniform Trade Secrets Act (TULSA) for possible misappropriation or infringement. b. Engaging legal counsel to handle trade secret litigation matters effectively, including seeking injunctive relief and damages. Types of Texas Checklists for Protecting Trade Secret Information: 1. Texas Healthcare Trade Secret Checklist: — Specific checklist tailored to the healthcare industry, considering unique trade secrets in medical practices, pharmaceuticals, and healthcare technology. 2. Texas Manufacturing Trade Secret Checklist: — Industry-specific checklist focusing on protecting trade secrets in manufacturing processes, designs, prototypes, supply chain management, and proprietary machinery. 3. Texas Technology Sector Trade Secret Checklist: — Tailored checklist for technology businesses, covering trade secrets related to software, algorithms, databases, copyrights, and technological advancements. Conclusion: Implementing the Texas Checklist for Protecting Trade Secret Information is crucial for businesses operating in Texas to safeguard their intellectual property rights effectively. By following these comprehensive guidelines and adapting them to specific industries or sectors, individuals and organizations can mitigate the risk of trade secret misappropriation, maintain competitiveness, and secure their assets in compliance with Texas laws.
Texas Checklist for Protecting Trade Secret Information
Description
How to fill out Texas Checklist For Protecting Trade Secret Information?
Discovering the right legitimate document template could be a have difficulties. Of course, there are a lot of templates available on the Internet, but how will you discover the legitimate kind you want? Make use of the US Legal Forms site. The services offers a large number of templates, like the Texas Checklist for Protecting Trade Secret Information, which you can use for enterprise and private needs. Every one of the varieties are checked by specialists and meet state and federal requirements.
If you are presently registered, log in to your account and then click the Acquire key to find the Texas Checklist for Protecting Trade Secret Information. Utilize your account to appear throughout the legitimate varieties you possess acquired in the past. Check out the My Forms tab of your respective account and have yet another duplicate from the document you want.
If you are a brand new end user of US Legal Forms, here are simple recommendations that you should adhere to:
- Initially, make certain you have selected the right kind to your city/county. You can look over the shape utilizing the Review key and read the shape outline to make certain it will be the right one for you.
- In the event the kind fails to meet your expectations, take advantage of the Seach field to find the proper kind.
- When you are sure that the shape is proper, click the Acquire now key to find the kind.
- Select the pricing strategy you need and type in the essential details. Create your account and purchase an order with your PayPal account or bank card.
- Choose the document file format and acquire the legitimate document template to your product.
- Complete, edit and produce and sign the attained Texas Checklist for Protecting Trade Secret Information.
US Legal Forms is the biggest library of legitimate varieties where you can see different document templates. Make use of the company to acquire expertly-manufactured documents that adhere to status requirements.