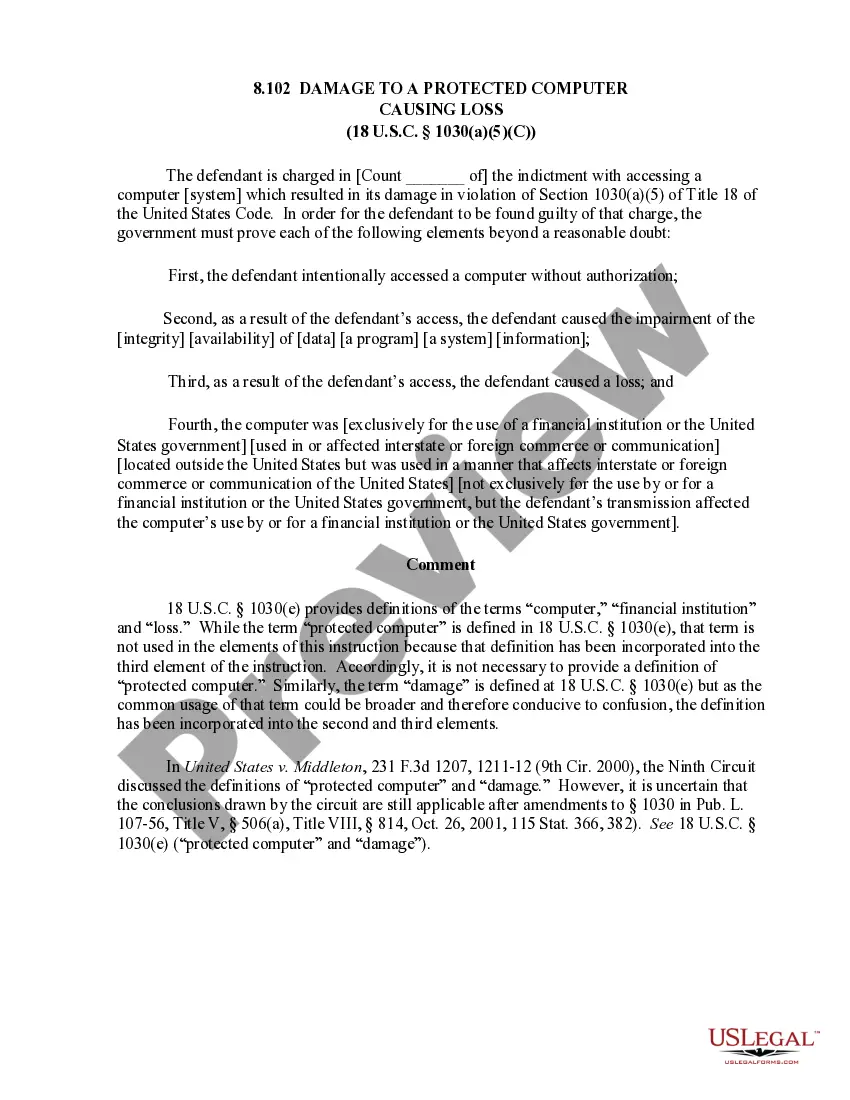
8.102 Damage to a Protected Computer Causing Loss (18 U.S.C. Sec. 1030(a)(5)(C)
Notarization guidance
In most cases, this form does not require notarization. However, some jurisdictions or signing circumstances might. US Legal Forms offers online notarization powered by Notarize, accessible 24/7 for a quick, remote process.
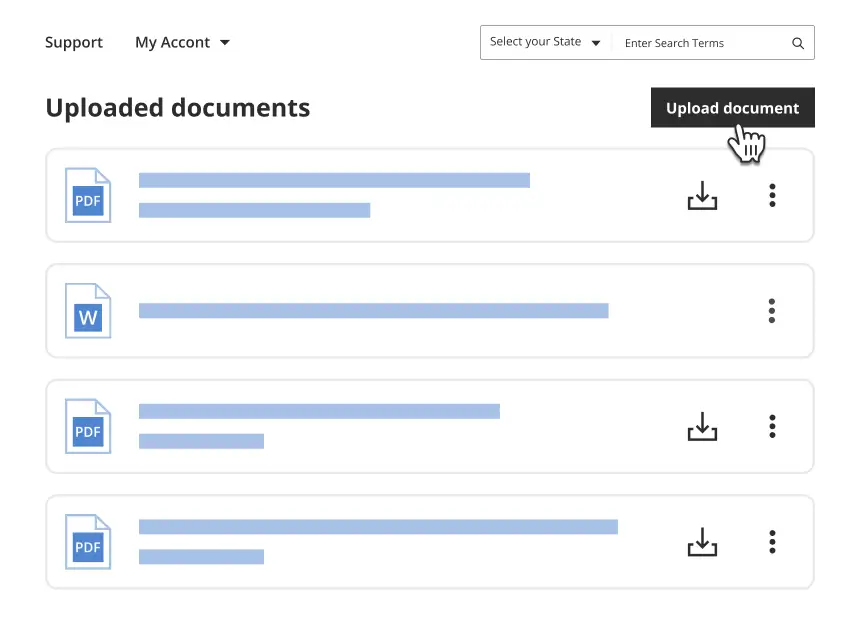
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
Form popularity
FAQ
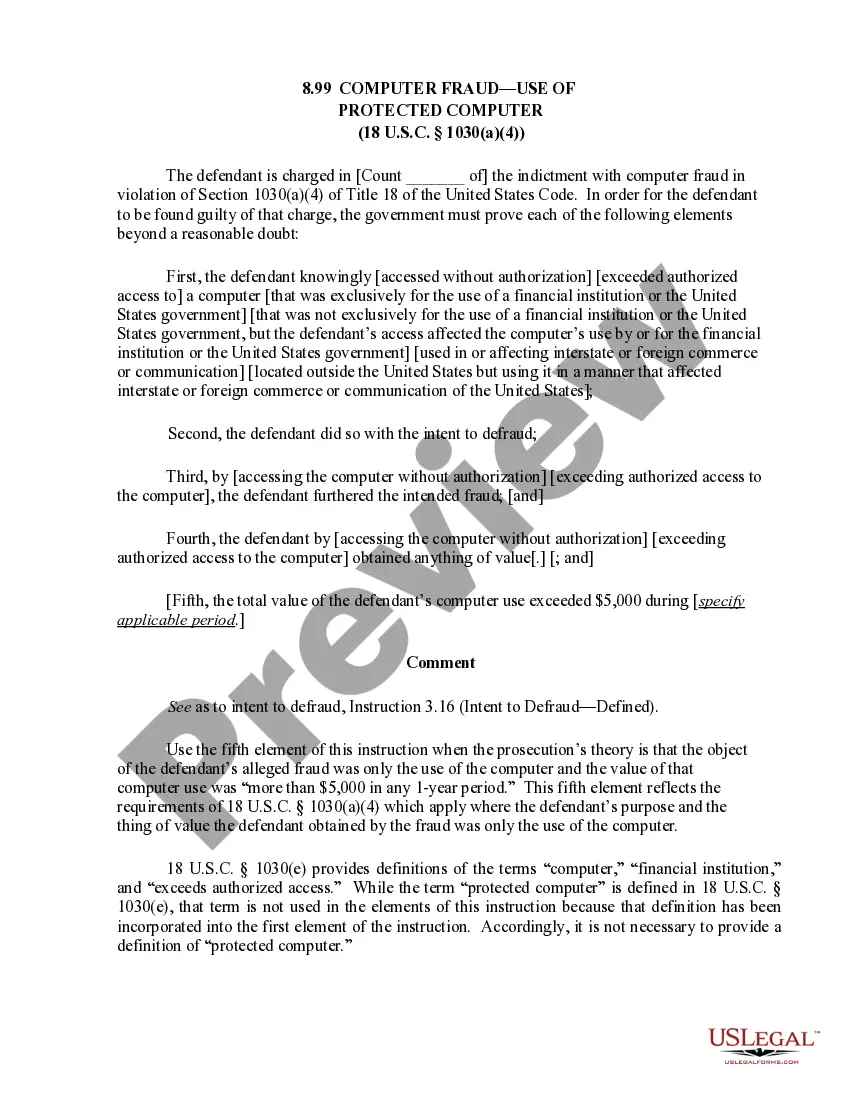
Computer Fraud and Abuse Act. In 1986, Congress passed the Computer Fraud and Abuse Act (CFAA), now codified under Title 18 U.S. Code § 1030. This law makes it a federal crime to gain unauthorized access to ?protected? computers (otherwise known as ?hacking?) with the intent to defraud or do damage.
1030, outlaws conduct that victimizes computer systems. It is a cyber security law. It protects federal computers, bank computers, and computers connected to the Internet. It shields them from trespassing, threats, damage, espionage, and from being corruptly used as instruments of fraud.
Unauthorized computer access, popularly referred to as hacking, describes a criminal action whereby someone uses a computer to knowingly gain access to data in a system without permission to access that data. Hacking is illegal under both California and federal law, and can result in heavy penalties.
In addition to imposing criminal penalties, the CFAA provides a private, civil cause of action for persons or entities harmed by a perpetrator's unauthorized access.
Criminal Penalties Under the CFAA OffensePenalties (Prison Sentence)Accessing a Computer and Obtaining InformationFirst conviction: Up to one year Second conviction: Up to 10 yearsIntentionally Damaging by Knowing TransmissionFirst conviction: Up to 10 years Second conviction: Up to 20 years4 more rows ?
§1030. Fraud and related activity in connection with computers. (C) intentionally accesses a protected computer without authorization, and as a result of such conduct, causes damage and loss.
The CFAA prohibits intentionally accessing a computer without authorization or in excess of authorization, but fails to define what ?without authorization? means. With harsh penalty schemes and malleable provisions, it has become a tool ripe for abuse and use against nearly every aspect of computer activity.
The Computer Fraud and Abuse Act (18 U.S.C. § 1030) (CFAA) imposes criminal and civil liability for unauthorized access or damage to a protected computer. The law reaches every computer connected to the internet and non-networked computers used by the US government or financial institutions.