8.97 Obtaining Information by Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)) is a federal law that prohibits the unauthorized access of a "protected" computer. A "protected" computer is defined as one that is used in interstate or foreign commerce or communication, affects interstate or foreign commerce or communication, or is used by the United States government. This law criminalizes the intentional access, without authorization, of a protected computer to obtain, alter, or damage information or to cause a “denial of service” attack. The penalties for this crime can include fines and jail time. There are two types of 8.97 Obtaining Information by Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)). The first type is the offense of obtaining information from a protected computer without authorization. This offense involves the unauthorized access of a protected computer to obtain information, whether the information is altered or deleted. The second type is the offense of damaging a protected computer. This offense involves the intentional damage, alteration, or destruction of information on a protected computer.
8.97 Obtaining Information by Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)).
Description
Get your form ready online
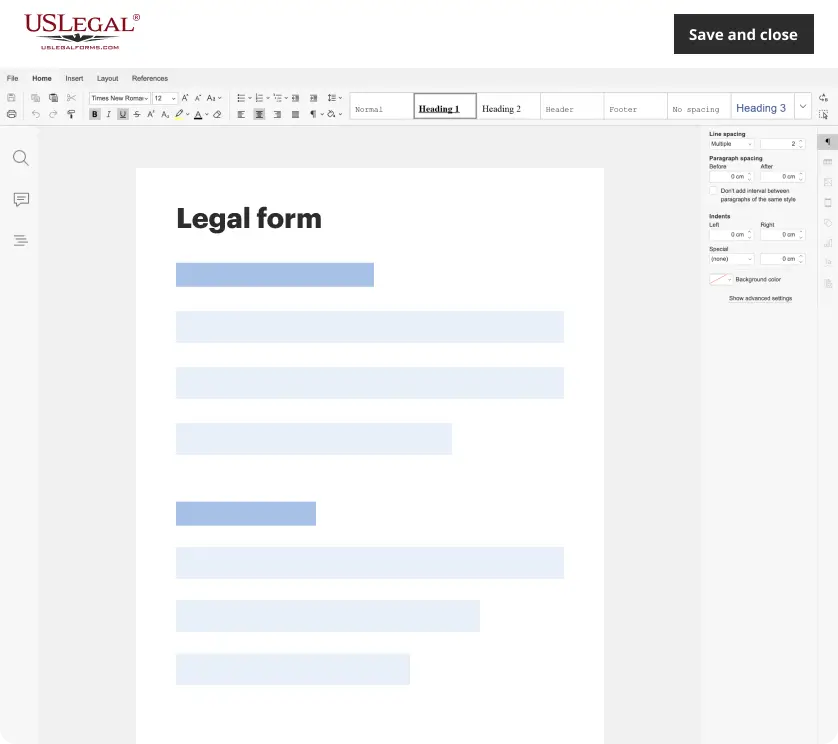
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
How to fill out 8.97 Obtaining Information By Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)).?
Dealing with legal documentation requires attention, accuracy, and using well-drafted templates. US Legal Forms has been helping people across the country do just that for 25 years, so when you pick your 8.97 Obtaining Information by Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)). template from our library, you can be certain it complies with federal and state laws.
Dealing with our service is straightforward and quick. To get the required document, all you’ll need is an account with a valid subscription. Here’s a quick guideline for you to get your 8.97 Obtaining Information by Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)). within minutes:
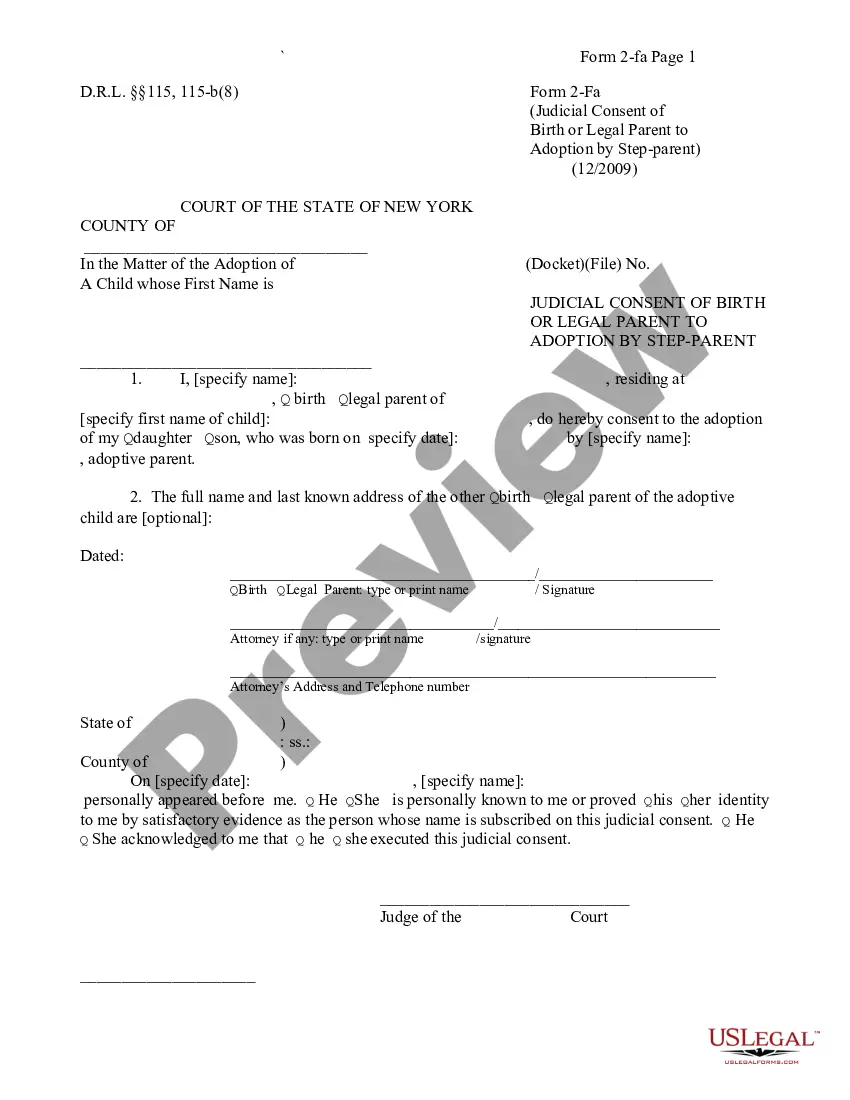
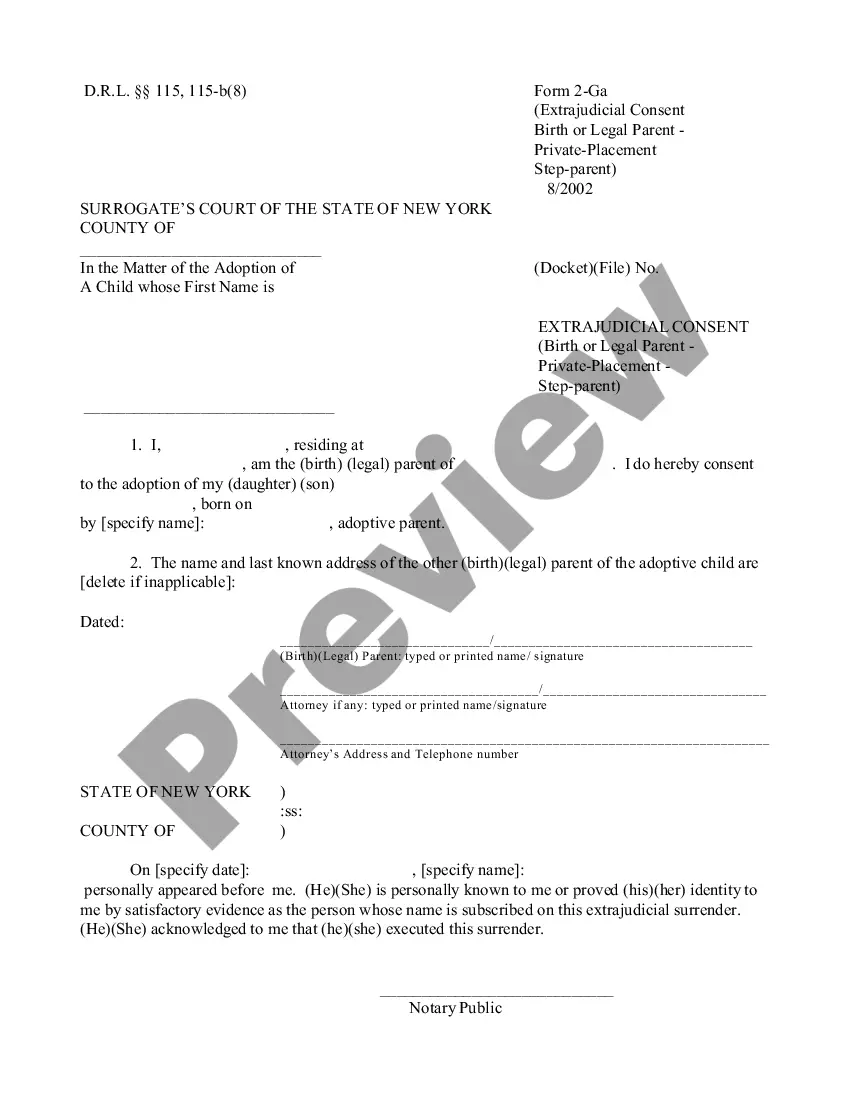
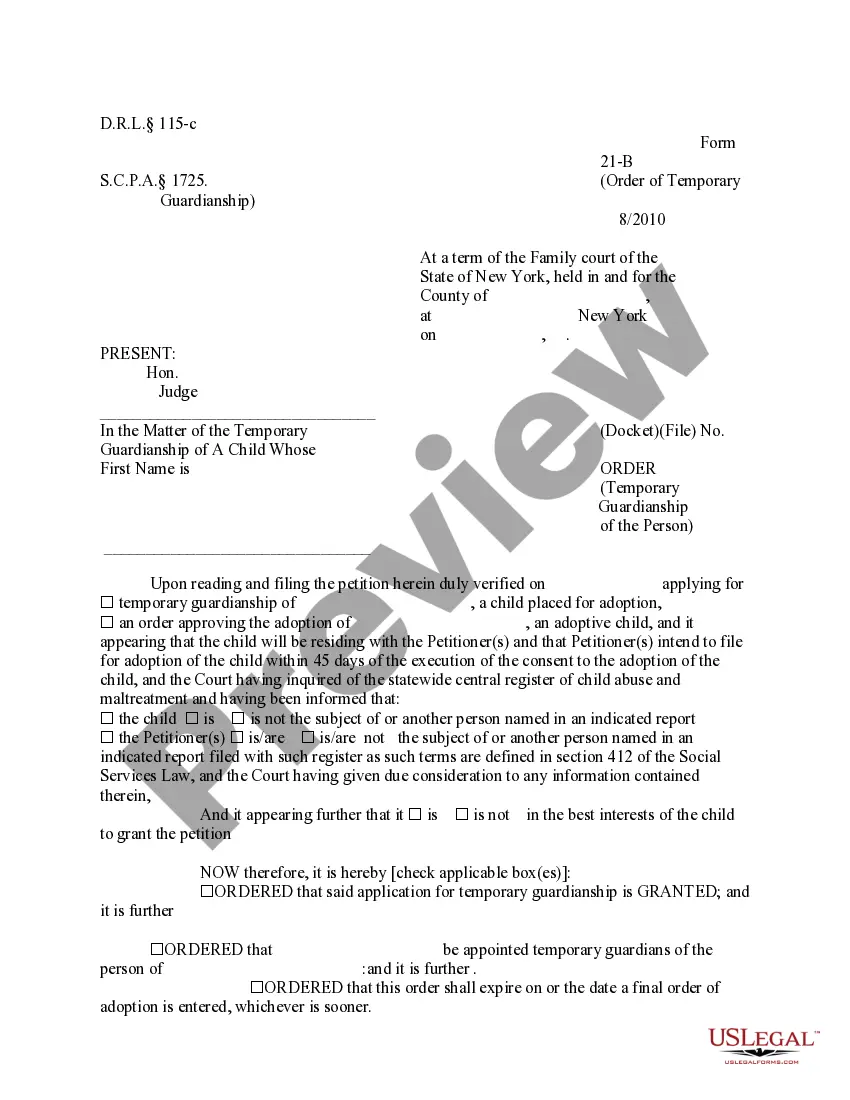
- Make sure to carefully check the form content and its correspondence with general and legal requirements by previewing it or reading its description.
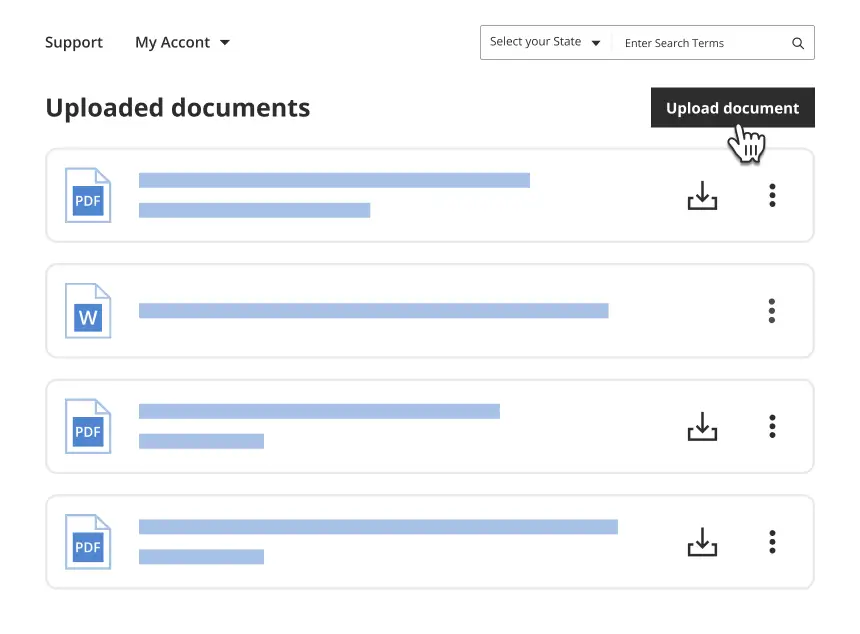
- Search for an alternative official blank if the previously opened one doesn’t match your situation or state regulations (the tab for that is on the top page corner).
- Log in to your account and save the 8.97 Obtaining Information by Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)). in the format you prefer. If it’s your first time with our website, click Buy now to continue.
- Register for an account, select your subscription plan, and pay with your credit card or PayPal account.
- Decide in what format you want to save your form and click Download. Print the blank or add it to a professional PDF editor to prepare it paper-free.
All documents are created for multi-usage, like the 8.97 Obtaining Information by Computer-"Protected" Computer (18 U.S.C. Sec. 1030(a)(2)(C)). you see on this page. If you need them in the future, you can fill them out without re-payment - simply open the My Forms tab in your profile and complete your document whenever you need it. Try US Legal Forms and prepare your business and personal paperwork rapidly and in total legal compliance!