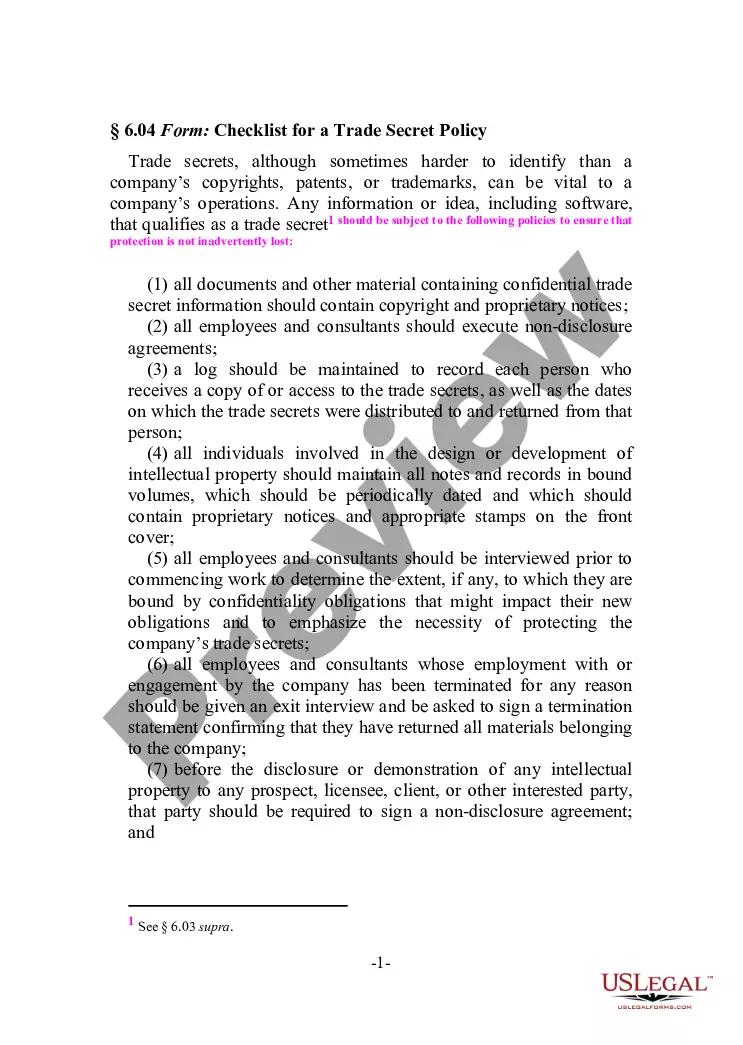
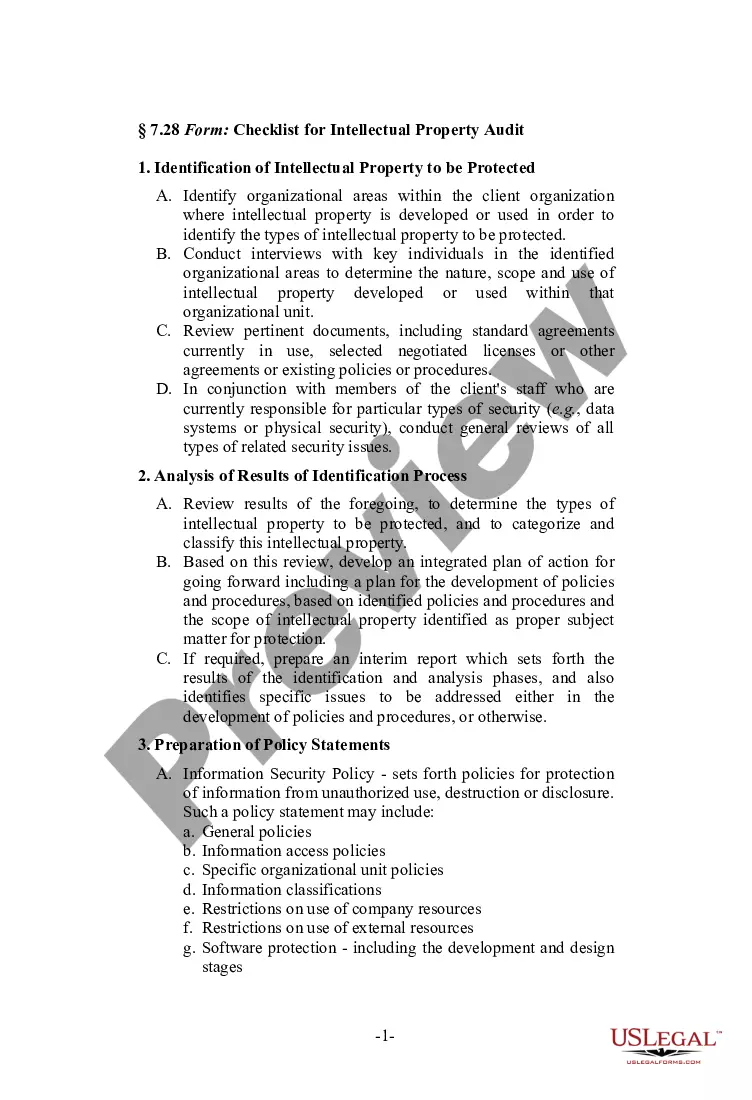
West Virginia Checklist for a Trade Secret Policy
Description
How to fill out Checklist For A Trade Secret Policy?
US Legal Forms - one of several largest libraries of authorized forms in the USA - gives a variety of authorized file web templates it is possible to down load or print out. Making use of the internet site, you can find a large number of forms for business and specific purposes, sorted by types, suggests, or search phrases.You can get the latest types of forms like the West Virginia Checklist for a Trade Secret Policy within minutes.
If you already have a monthly subscription, log in and down load West Virginia Checklist for a Trade Secret Policy from the US Legal Forms catalogue. The Acquire button will appear on each type you see. You have access to all in the past downloaded forms from the My Forms tab of your respective accounts.
If you wish to use US Legal Forms the very first time, allow me to share straightforward directions to help you get started off:
- Be sure you have picked out the best type for your town/state. Select the Review button to analyze the form`s content. Read the type description to ensure that you have chosen the right type.
- In case the type does not match your demands, make use of the Lookup field on top of the display to discover the the one that does.
- Should you be content with the shape, verify your selection by clicking the Get now button. Then, choose the costs prepare you want and supply your qualifications to sign up to have an accounts.
- Approach the purchase. Utilize your bank card or PayPal accounts to accomplish the purchase.
- Find the file format and down load the shape on the gadget.
- Make adjustments. Fill up, change and print out and indicator the downloaded West Virginia Checklist for a Trade Secret Policy.
Each and every design you put into your bank account lacks an expiration date which is your own property for a long time. So, if you would like down load or print out yet another version, just proceed to the My Forms section and click around the type you need.
Gain access to the West Virginia Checklist for a Trade Secret Policy with US Legal Forms, probably the most extensive catalogue of authorized file web templates. Use a large number of professional and condition-certain web templates that satisfy your company or specific needs and demands.
Form popularity
FAQ
It must have actual or potential commercial value because it is secret. It must have been subject to reasonable steps by the rightful holder of the information to keep it secret (e.g., through confidentiality agreements).
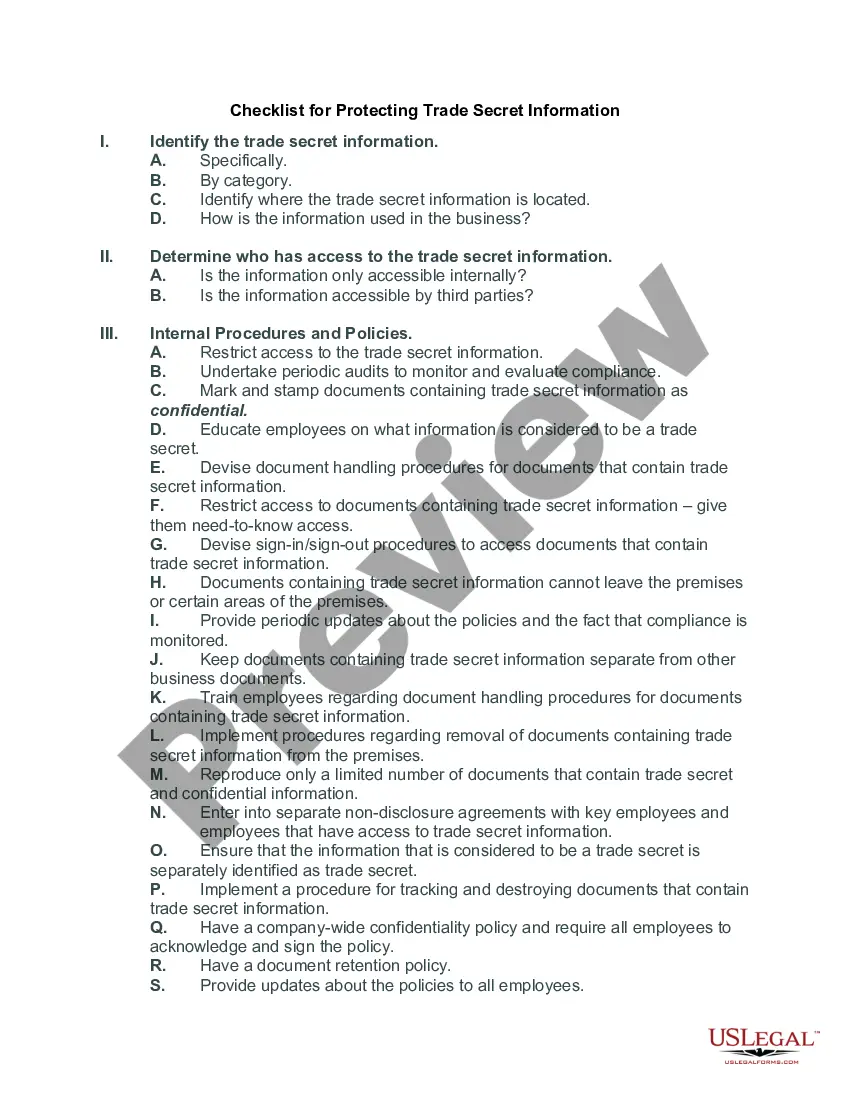
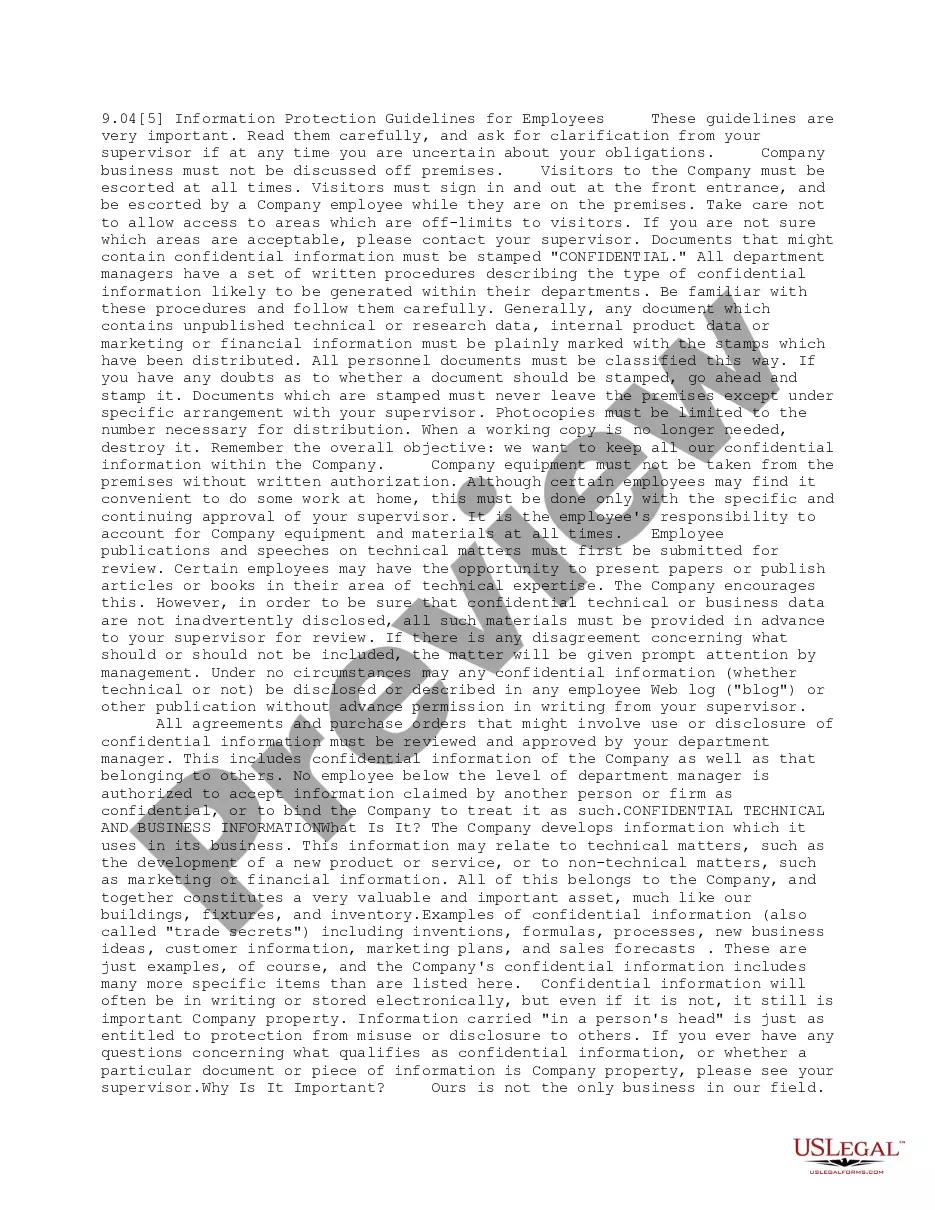
Hear this out loud PauseYour company's trade secrets ? in paper or electronic format ? should be accompanied by a confidentiality notice. Each page should be stamped ?Confidential.? The notice should notify all parties that the document includes trade secrets and that access to the information is limited by your business.
· Rule: For a trade secret to qualify for protection, it must meet the following three elements: Subject matter must be trade secret (INFORMATION) Economically valuable - can be determined by what company did to protect it; competitive advantage. A "secret"
Hear this out loud Pause"Trade secret" means any method, technique, process, formula, program, design, or other information that can be used in the course of production, sales, or operations that can also meet the following three requirements: (1) it is not known to persons generally involved in the information of this type; (2) it has actual ...
A trade secret is information that: is not generally known to the public; confers economic benefit on its holder because the information is not publicly known; and. where the holder makes reasonable efforts to maintain its secrecy.
Hear this out loud PauseIn general, a trade secret has three parts: (1) information (2) economic value from not being generally known by others, and (3) reasonable efforts have been taken to protect the trade secret.
In general, a trade secret has three parts: (1) information (2) economic value from not being generally known by others, and (3) reasonable efforts have been taken to protect the trade secret.
Hear this out loud PauseIn general, to constitute a trade secret under these various laws (which each have their own nuances), the information must (1) have economic value; (2) because it is not generally known; and (3) the owner has taken reasonable measures to keep the information a secret.